More than 6 out of 10 businesses were subjected to phishing and social engineering attacks last year, and as cybersecurity becomes a larger concern for established businesses and startups, we can expect that number to increase dramatically in 2020 and through the decade to come.
While established companies frequently face attack attempts, it’s actually startups who are the most at risk. Because other issues like rapid business growth and customer acquisition seem more pressing than securing data, startups are the victims of data breaches 58% of the time, making security for startups all the more important.
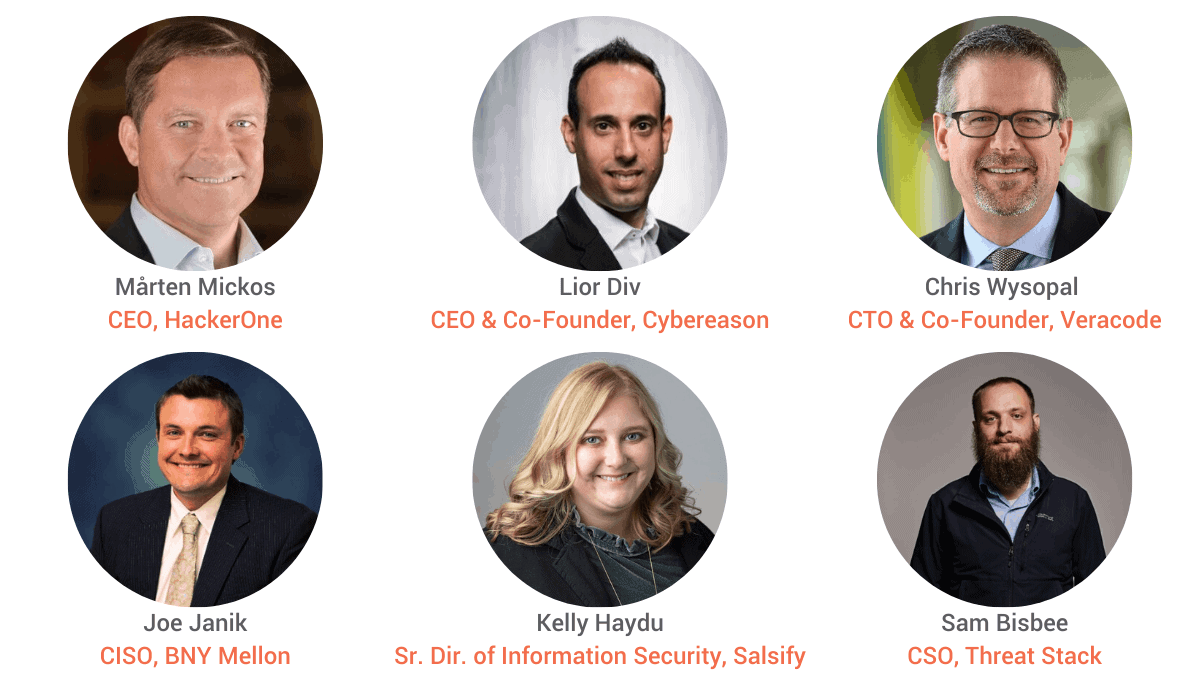
To help entrepreneurs understand the seriousness of cyber threats, we sat down with six executives at the 2019 Core Summit who shared their experiences and tips for avoiding security issues and explored how a startup might turn security into an advantage rather than a burden. The panelists were: Mårten Mickos, CEO of HackerOne, Lior Div, CEO and Co-Founder of Cybereason, Chris Wysopal, CTO and Co-Founder of Veracode, Joe Janik, Former CISO of Acquia, Kelly Haydu, Senior Director of Information Security at Salsify, and Sam Bisbee, CSO at Threat Stack.
Read on for their advice on data privacy, transparency in sharing data between companies, innovation in cybersecurity, ensuring security in the sales process, and much more.
How do companies see security as a competitive advantage?
Chris Wysopal noted that questions from prospects about security – while legitimate – “definitely slow down the sales cycle,” but that this should inspire companies to have clear processes and answers surrounding data security for customers.
“Having the right security controls in place – [and] having a really good way to communicate them – is a competitive advantage, because it speeds up your sales cycle,” he said.
Kelly shared that “one of the things that we’ve done at Salsify is put together a security package that has pre-populated questions and answers about the security of our organization.”
“It gives somebody that’s doing a risk assessment on us the level of comfort that they need in order to know that we’re securing their data,” she said. “And it really, really helps when you have that given to a CISO at a large organization like a Coca Cola or a L’Oreal to say, ‘hey, they have all of these boxes checked.’”
Lior shared that companies that focus on security will benefit from a healthy brand perception. In his eyes, companies are split into two groups: those that are on the defensive, and “the more sophisticated organizations that actually use security to say, ‘we want to be a better brand, and that’s going to give us a competitive edge on our competition.’”
What are your thoughts on the innovation of new security, and how do we design security safely?
Lior mentioned the fact that since hackers are constantly innovating, cybersecurity teams in companies must do the same.
Mårten believes that companies should focus on a front-line of defense before trying to innovate on solutions that may not fully work.
“You have so many other problems to solve before that,” he said. “ I advise customers to just think of ways in which you can act faster.
He went on to ask, “if there’s a breach, how fast will you know about it? If there’s a threat, how soon can you know about it? If there is something wrong, how soon can you fix it?”
How did the panelists see cybersecurity being handled within organizations?
Sam Bisbee of Threat Stack noted the pressure that new companies face as they scale quickly – especially in his own startup.
“The fact that we have 15 to 20 people in the security team at a startup is unheard of. There are public companies with security teams smaller than the team that I run.”
Mårten Mickos of HackerOne advocated for a tool he’s using to avoid cybersecurity threats in his own company. “We use KnowBe4 for anti-phishing training. Every now and then, I get these weird emails,” he said, “and I send it to an [information security] email address, and then they will validate whether I was correct.”
“Just this simple thing – It makes me think about phishing all the time,” he admitted.
Lior explained how he felt the pressure from a different source. “Actually, we are using a different service. It’s called the Chinese. They’re testing us all the time – all the time. It’s free.”
“But they don’t tell you when you fail,” Mårten replied to Lior. “That’s the difference.”
When you’re looking to bring on a new security solution, how do you differentiate products, and how do you address the gaps between products and your organization?
Joe Janik recommended startups and established companies fail fast when determining a new vendor.
“Make sure on an annual basis you review what the value [of the] return on investment was,” he suggested. “Know what value perceived…is actually working in your environment. If not, look to collapse, look for other toolsets, or invest in your teams and make sure that they’re innovating.
Sam Bisbee noted his team would prefer to tweak whatever solution they determine best fits his company wherever possible. “We did not go buy a security orchestration automation vendor, because we’ve got engineering and coding talent in the security team. So, it made more sense for us to go grab a small ‘If This Then That’ framework, plum our telemetry into it, and start tailoring it to our own organization.”
However, he encourages companies to note their shortcomings and seek security help where it’s needed.
“As far as detecting or responding to something happening on a corporate endpoint, [that’s] not our center of excellence. But according to the gap analysis we did, it was a critical control that we needed. So, we went and outsourced that effectively, because we have to acknowledge the same conversation that we have with our customers, which is: Do you want to be a security company or a secure company?”
''...we have to acknowledge the same conversation that we have with our customers, which is: Do you want to be a security company or a secure company?'' - @sbisbee, CSO of @threatstack on what startups should outsource or tackle… Share on X
How can the CISO’s share their silos of data without threatening privacy?
The panel discussed that companies – especially startups – are eager for information and statistics on data and privacy, but recognize that in order to receive, you sometimes have to give.
Kelly Haydu of Salsify noted: “By not sharing that information, it actually becomes more of a problem later on down the road,” noting that everyone wants people to share data…until it’s their own.
“We see a lot of times that security holds back in portraying information and potential data breaches or mistakes,” she said.
Kelly’s proposed solution for balancing transparency and anonymity in data comes from peer sharing. “We all have to get together and start to form trust groups where we can share that information, and know that it is in that four walls, and that we can continue to work forward.”
Joe Janik, formerly of Acquia, noted that transparency starts internally. “The first precondition is that you’re sharing your functions within your own teams and within your own company,” he said. “Make sure that you empower the service delivery teams [and] the product teams to actually own and be tuned into their products as to what security events are relevant to them.”
“Share that information across your service teams,” he said. “Empower them. Have them have ownership of some of that security aspect of delivering their service.”
Chris Wysopal of Veracode, however, noted the difficulty that newer companies face when sharing data internally. “Most organizations – especially when you talk about inter-organization sharing – are just not mature enough to do that. They don’t have the capability to do that,” he said.
Lior Div of Cybereason advocated for transparency and how helpful it can be to other companies. “I do think the sharing is caring,” he said.
Pushing the idea further, he said, “forget about the mechanism of what you can or cannot share. What do you share, and what piece of information actually can help somebody else do something about it? Because if I’m just sharing that I was under attack, I’m not sharing what was exactly the nature of the attacker, [or] what the hacker did. lt’s really not helping.”
However, Lior did acknowledge that it’s difficult for this expectation to be a reality. “The concept of sharing is critical for the success of this community,” he said, “but I think that we’re not there yet in terms of the mechanism of how to share, and what to share, and what to do with the information.”
——–








